Ajmal Anwar
IT & Cyber Security Enthusiast
Where Values Meet Technology
I’ve always believed that Sincerity and Honesty are more than values - they’re tools, just as essential as any Firewall or SIEM I use today. They guide the way I work, the way I take responsibility, and the way I protect the systems and people entrusted to me.I didn’t enter technology through textbooks or perfect scores.
I entered it through curiosity - the kind that made me open every toy, radio, and electronic device at home just to understand what lived inside. That curiosity became my compass.It carried me into IT, strengthened me through years of real-world challenges, and eventually led me into Cybersecurity - a place where every day feels like a blend of investigation, learning, and defending. A place where curiosity finally found its purpose.Today, Cybersecurity isn’t just my profession; it’s my responsibility. A responsibility to build safer environments, protect identities, and guide people toward better digital habits - always with integrity at the center.
======================
== EXPERIENCE.LOG ==
======================[BOOT] Initializing 2010 → 2025 career timeline…
[✓] Networking stack loaded
[✓] IT operations stable
[✓] Cybersecurity engine activated[2010-ROLE] System Administrator role activated. Managing 25+ user environment.
[2010-LOC] India → Local infrastructure support stabilized.[2011-WIPRO] Deployment to Wipro environment initiated.
[2011-USERS] Handling 1500+ users across 35 concurrent projects.
[2011-OPS] Desktop | Network | Datacenter operations online.[2014-UAE-MOVE] Environment switch detected → UAE Hospitality Sector.
[2014-HOTELS] Supporting 7 hotel properties with 24/7 operational uptime.
[2014-NOC] High-availability support mode enabled.[2017-SOLO-OPS] Transition to independent IT administrator role.
[2017-FULLSTACK] Managing infrastructure, servers, security, backups, and guest networks.
[2017-LOAD] Single-operator mode: 100% responsibility | 0 escalations forward.[2020-UPGRADE] System update triggered → Learning phase initiated.
[2020-TRAINING] Networking | Email Security | SOC | Threat Detection | Cloud Security modules downloaded.[2021-CYBER-PIVOT] Role transition: IT Infrastructure & Security Analyst activated.
[2021-SOC] Monitoring, vulnerability management, email gateway protection online.[2021→2025-SECURITY-PROJECTS] Major transformation projects executed.
[SEC-001] SIEM customization + use-case detection logic deployed.
[SEC-002] Email Gateway enhancements (Mimecast) online.
[SEC-003] PAM evaluation + access hardening processes enabled.
[SEC-004] Threat monitoring & incident response workflows optimized.[STATUS] Experience logs updated successfully.
[READY] Awaiting next command…
IT INFRASTRUCTURE & SECURITY ANALYST | 2021- Present, Dubai-UAE
• Monitor, investigate, and respond to security alerts and incidents.
• Execute threat hunting, malware analysis (basic), and log analysis across
endpoints, servers, and cloud systems.
• Conduct vulnerability scanning, reporting, and remediation follow-ups with
stakeholders.
• Lead PAM solution evaluations; improve access control and privilege
governance.
• Manage enterprise email security (DMARC, SPF, DKIM, anti-phishing).
• Deliver internal cybersecurity awareness campaigns (Trainings, Policies,
Posters, Slack, Email reminders).
• Support servers, networks, cloud systems, backups, DR planning, and IT
audits.
IT ADMINISTATOR & INCHARGE | 2015-2021 - Dubai, UAE
• Managed IT infrastructure including servers, networks, firewalls, Wi-Fi,
backups, and endpoint
devices.
• Supported hotel applications: Opera PMS, Micros POS, FMC, Sun Systems HRnet.
• Performed system audits, patching, DR testing, and vendor coordination.
• Delivered 24/7 support for major IT incidents with full SLA compliance.
• Managed procurement, asset control, documentation, and vendor evaluations.
Data Centre Operations Engineer | 2014-2015 - India
Managed core banking data center operations and Solaris server
environments.
• Handled backups using LTO, DAT, DDS tapes; monitored BOD/EOD processes.
• Monitored ATM, internet banking, and secure messaging systems.
• Coordinated with DB and application teams; resolved infrastructure issues.
Desktop & Network Engineer | 2011-2014 - India
• Supported desktop & network issues, user accounts, DNS/DHCP, IP
configuration.
• Assisted with system backups and OS restoration tasks
IT Intern - Systems Admin | 2010-2011 - India
• Troubleshooting network and desktop related issues.
• Creating and Managing user accounts & groups.
• User control restrictions for sharing files & folders.
• DNS & DHCP configuration and administration.
• Configuring and troubleshooting IP address schemes.
• Backup and restoration of operating systems.
Digital Shield Wall (Certifications)
I’ve always believed that real understanding comes from doing. Books and theories give us a foundation, but for me, true confidence comes only when I can put my hands on something, break it, fix it, and see how it works in real scenarios. That’s the way I learn best - by connecting concepts to practical action.At the same time, I know how important industry-standard certifications are, both for validating skills and for growing in this field. Earning the certifications below has helped me strengthen my knowledge, stay disciplined, and build more trust in the work I do. They serve as milestones in my journey, not just achievements.
[MICROSOFT SC-100] Cybersecurity Architect
[MICROSOFT SC-200] Security Operations Analyst
[MICROSOFT SC-900] Security Fundamentals
[EC-COUNCIL CEH] Certified Ethical Hacker
[MIMECAST ] Email Security Advanced
[FORTINET NS2] Network Security
[SPLUNK] SIEM Analysis Fundamentals
(CISCO) Certified Network Associate
My Defense Stack (Technical Skills)
Cloud & Cyber Security:
Cybersecurity Awareness Campaigns, ISO 27001 Awareness, Data and Email Security, AWS, Azure & Oracle Cloud Practice, Audit & Compliance, Ethical Hacking.Cybersecurity Hands-On Tools:
Firewalls, SIEM, Email Security, Data Leak & Brand Protection, EDR & Incident Response, IAM, Monitoring & Patch Management, Password Manager, Encryption, MFA, Security Awareness Training & Phishing Campaign, Data Transfer, Documentation.Security & Vulnerability Audits:
IT Vulnerability Monitoring, Analysis and Reporting, Risk Assessments, Incident Management and understanding of Vulnerability tools – Tenable Nessus and SplunkHardware Installation, Configuration & Administration:
Servers, Workstations, Printers, Firewall, Routers, Switches, Biometric Devices, PABX, Wireless Controllers, APs, Internet Gateways, POS, IP Phones, IPTV, Projectors.Application Installation & Management:
Windows Server & Workstations OS, Linux OS, Apple OS, Applications such as ERP, Finacle, Oracle DB, Solaris, Symantec, Veeam, Acronis, VMware, Citrix, Opera PMS, Micros, FMC, Tiger, ERP, Cisco, Fortinet, Office 365, Office Suits and various project-oriented applications.Backup & Maintenance:
Routine backup procedure based on retention for Devices & User Data Files. Maintaining Backup
Storages and backup tapes. Backup Application installation and maintenance.Upgrades & Audit:
Routine updates and auditing for the various systems and hardware devices.Asset Management:
Proper allocation of hardware and software for each department and maintaining the documentation.Customer Support & Troubleshooting:
Handling customer requirements and queries and the rectification of issues within
the SLA.Projects Implementation & Execution:
Planning, execution and testing of new projects and requirements set by the company.
The Other Side of Me —
The Creator, Explorer & Story Collector
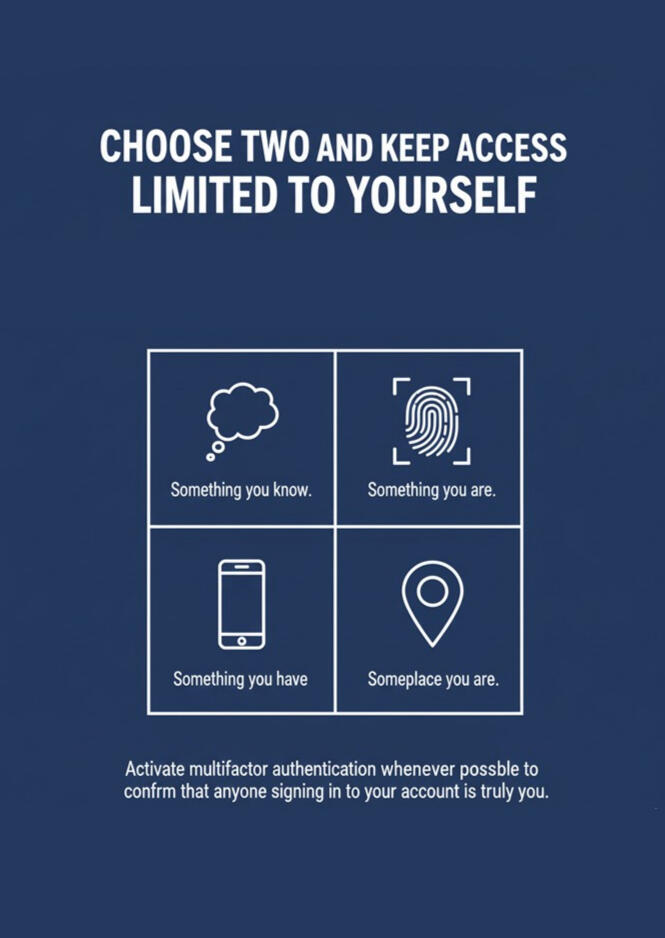
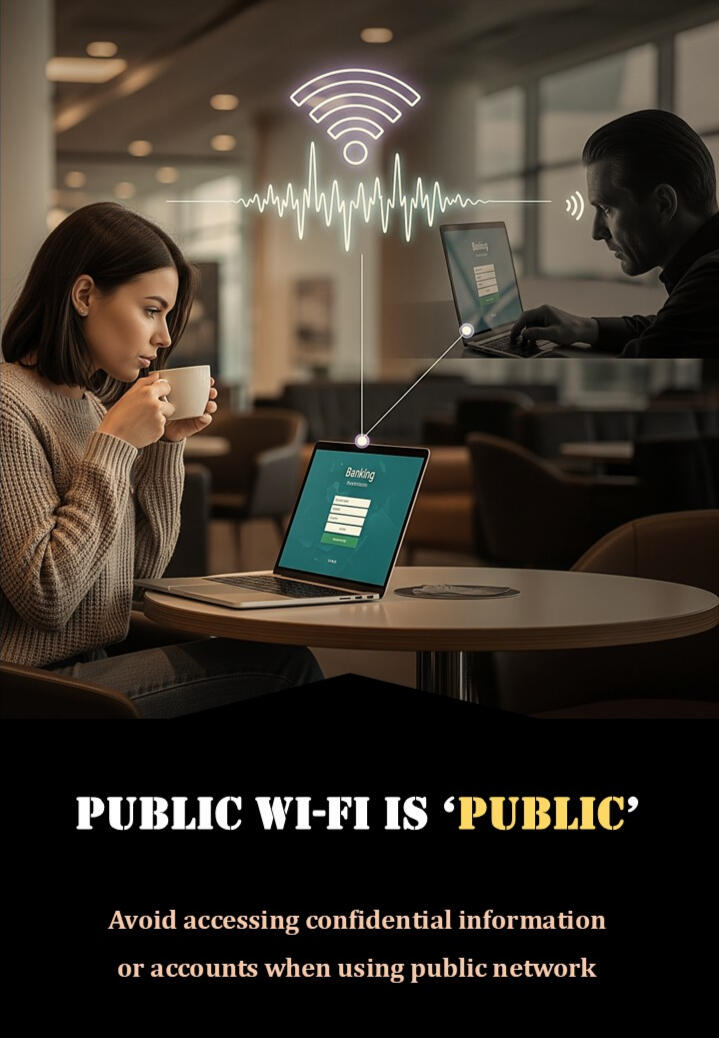
Outside of work, I am a creator, explorer, and lifelong learner. I’ve always been drawn to discovering new ways to do things — experimenting with apps, building small digital tools, designing visuals, and finding smarter ways to make life easier. Exploring new platforms, testing automation, or simply imagining a better workflow gives me energy and keeps my curiosity alive.Photography is another part of my world. I love capturing landscapes and architecture, freezing moments that tell stories, and sharing glimpses of the world I see. Traveling through Georgia, Armenia, Oman, and Azerbaijan opened my eyes to different cultures, perspectives, and experiences — enriching my creativity and giving me fresh ideas to bring into both life and work.This curiosity and creative energy naturally found its way into my cybersecurity journey. I realized that protecting systems isn’t just about technology — it’s about people and awareness. To bridge this gap, I began designing security awareness posters for my teams. Each poster is crafted to be engaging, clear, and memorable, turning complex security concepts into something human, relatable, and actionable.From phishing simulations to password hygiene, from email security to data protection, these posters help teams stay vigilant and confident. Seeing colleagues use them, reference them, and take proactive steps gave me a sense of fulfillment I didn’t expect. It reminded me that creativity and cybersecurity can work hand in hand — and that human awareness is just as vital as any firewall or SIEM I manage.In my world, curiosity fuels creativity, and creativity strengthens protection. Whether it’s exploring the digital landscape, capturing a perfect photograph, or designing tools and awareness campaigns, these passions all feed into one mission: making technology safer, smarter, and more human.
Through my lens
Photography has always been a quiet space for me - a way to pause, observe, and capture moments that often go unnoticed.
Beyond cybersecurity and technical work, this is something that helps me stay grounded, creative, and connected to the world around me.This page is simply a collection of images I’ve captured over time.
No theme, no rules - just the way I see things through my own lens.Some photos reflect calm moments, some reflect movement, and others just reflect curiosity. Together, they tell a small story of the places I’ve seen and the moments I wanted to remember.I’ll be adding more pictures as I continue exploring, learning, and noticing the little things around me.Thanks for stopping by and taking a look.
— Ajmal
Security Awareness Through Design
Cybersecurity awareness is often delivered as long sessions, one-time workshops, or presentations that people attend because they must. These formats have value, but they don’t always stay with people in a practical way. True awareness takes root only when the message is simple, relatable, and easy to remember during everyday work.Over time, while supporting users and observing how they reacted to different types of guidance, one pattern became clear:
short, meaningful reminders were far more effective than lengthy explanations.That understanding eventually shaped an initiative called Creative Defense — a small, continuous effort to keep security visible through weekly, bite-sized posters. Each poster focuses on a single idea that someone can absorb in a few seconds, without feeling overwhelmed.The designs are inspired by real situations: phishing attempts users encounter, common mistakes seen across organizations, ongoing global threats, and practical tips drawn from day-to-day work. The intention is not to replace formal training, but to complement it with something simple, visual, and consistent.The response has been positive. Colleagues found the approach easier to connect with, and many mentioned that these quick reminders helped them apply safe practices more naturally. That feedback reinforced the idea that awareness works best when it becomes part of the culture — not an annual checkbox.Creative Defense continues to grow as new threats and learning opportunities appear. Each poster reflects a belief that security awareness should be accessible to everyone, delivered in a way that encourages people to understand, remember, and act — without pressure, judgement, or complexity.Below is the ongoing collection of some of the posters which I created as part of this initiative - a set that continues to grow as new situations, stories, and real-world threats emerge.
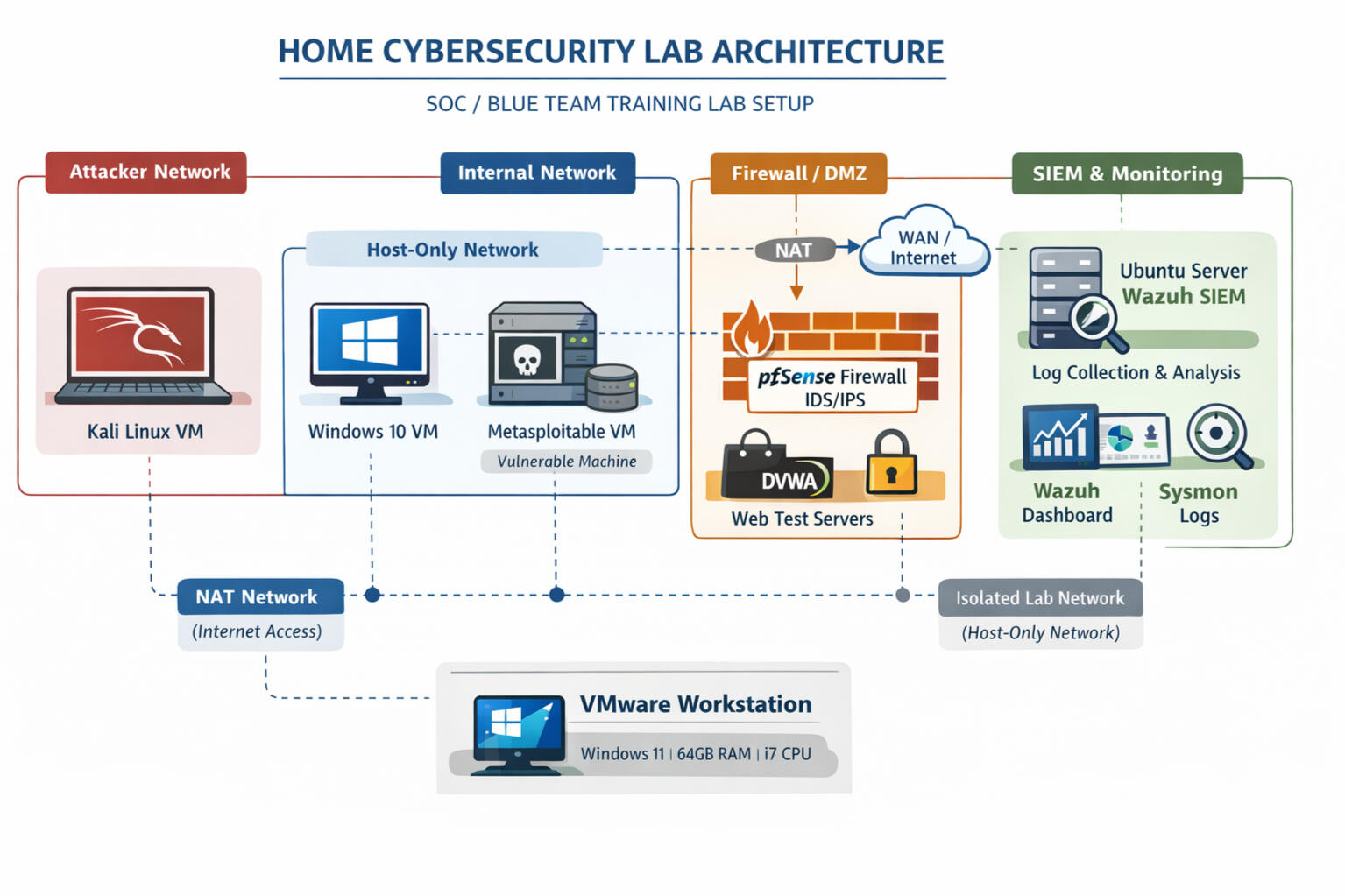
Research Zone: ZyberLab by Ajmal
A hands-on learning project where I’m building a complete, enterprise-style cybersecurity lab from scratch.This lab helps to understand real-world IT infrastructure, security monitoring, threat detection, and SOC workflows through practical, step-by-step implementation. I’m documenting each stage in a simple, structured way so anyone -beginners or professionals can follow along, learn, and even build the same setup if they wish.What This Lab Includes:
* Active Directory, DNS, DHCP
* Windows & Linux endpoints
* Wazuh SIEM + Sysmon
* SOC analyst workflows
* Network segmentation
* Web application security labs (DVWA, Juice Shop)
* Troubleshooting guides & KB pagesThis project continues to grow as I add new components, detections, and learning notes over time.
Refer to my detailed documentation page for more information: